Govern Once, Satisfy Many: A Framework-Agnostic Model for Cybersecurity Governance
Govern Once, Satisfy Many: A Framework-Agnostic Model for Cybersecurity Governance
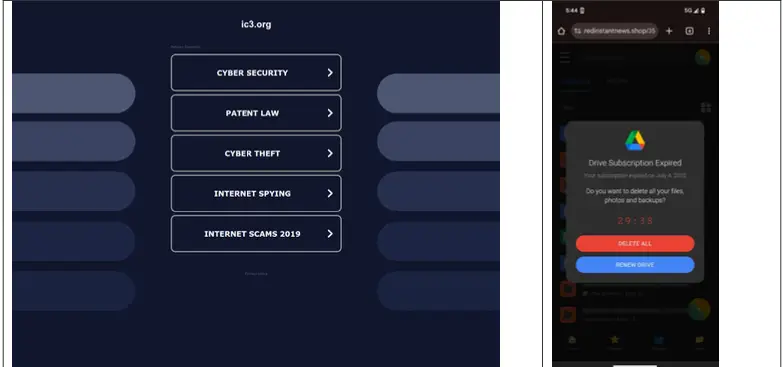
Most organizations juggle multiple cybersecurity frameworks—NIST CSF, ISO 27001, SOC 2, FedRAMP, CMMC—each with its own controls and audits. This creates a patchwork of overlapping efforts that drain resources and blur accountability. Framework-agnostic governance offers a smarter path, turning complex requirements into unified, audit-ready operations. In this post, you’ll see how GovSecure360 streamlines compliance while strengthening your security posture without adding tool sprawl. For more information, visit this guide on cybersecurity frameworks.
Framework-Agnostic Governance Benefits
Imagine turning a maze of compliance standards into a single, clear path. Framework-agnostic governance does just that, simplifying compliance across various standards by harmonizing operations.
Unified Compliance Across Standards
You may think multiple frameworks mean multiple headaches, but it doesn’t have to. With framework-agnostic governance, you can manage all these frameworks without the chaos. By using a single approach, you can meet the needs of NIST CSF, ISO 27001, and others efficiently. This strategy reduces duplicate efforts and helps you focus on what really matters—securing your data. Many businesses have already found that this unified approach saves both time and resources.
Operational Security Improvements
Stronger security doesn’t need to be complicated. A streamlined approach helps you spot and fix vulnerabilities faster. By focusing on core security practices, rather than juggling different standards, you improve your defenses. This method also enhances team collaboration, ensuring everyone is on the same page. You gain a clearer view of your security landscape, which makes it easier to address threats promptly.
Audit-Ready Operations and Defensibility
Being prepared for audits is crucial. A framework-agnostic model allows you to maintain an audit-ready state continuously. This readiness helps defend your organization during reviews and reduces the stress associated with unexpected audits. The more you integrate and automate your compliance efforts, the more defensible your systems become.
Implementing a Cybersecurity Governance Model

Transitioning to a new governance model might sound daunting, but the rewards are worth it. By leveraging AI and automation, you can simplify this process and achieve continuous compliance.
AI Governance Intelligence and Automation
Artificial intelligence can be your best ally in managing complex governance tasks. It helps in predicting risks and automating responses, which frees up your team for other critical tasks. AI-driven tools can analyze data more accurately and faster than humans, providing you with actionable insights. This ensures that your governance model adapts to new challenges swiftly.
Control Mapping and Evidence Automation
Automated control mapping connects the dots between requirements and actions. This process eliminates manual errors and provides accurate evidence of compliance. Automation also ensures that no aspect of your governance is left unchecked. By automating evidence collection, you save time and reduce the risk of non-compliance.
Policy as Code and Continuous Compliance
Transforming policies into code allows for real-time compliance checks. This method integrates policy checks into your daily operations, ensuring that you remain compliant without additional effort. Continuous compliance means peace of mind, knowing that you’re always audit-ready.
GovSecure360: Your Trusted Partner
When it comes to cybersecurity, having a trusted partner makes all the difference. GovSecure360 offers a comprehensive solution that integrates security, governance, and trust.
Secure Cloud Architecture and TrustOps
A secure cloud architecture provides a robust foundation for your operations. With GovSecure360’s TrustOps, you gain transparency and control over your cloud environment. This platform ensures that your data remains secure, regardless of where it’s stored. TrustOps offers continuous monitoring, giving you the confidence that your systems are protected against threats.
Risk Management and Zero Trust
Effective risk management requires more than just identification—it demands action. GovSecure360 implements a Zero Trust approach, meaning every access request is verified and authenticated. This strategy minimizes risk and enhances security. By adopting Zero Trust, you take proactive steps to protect your assets.
Workshop Offer: Governance Mapping and ROI Estimate
Understanding the value of your cybersecurity investments is crucial. GovSecure360 offers a workshop to map your governance needs and estimate the ROI. This session provides insights into how a framework-agnostic model can benefit your organization specifically. By participating, you can make informed decisions about your cybersecurity strategy.
In conclusion, adopting a framework-agnostic model simplifies compliance, enhances security, and prepares you for audits. With the support of GovSecure360, you can confidently navigate the complexities of cybersecurity governance, ensuring your systems are both secure and efficient.